Beware of emails with file attachments! There is a zero-day vulnerability that allows malicious code to be downloaded and executed via Word documents. There is not yet an official update to close the security gap.
Folina vulnerability
The German Federal Office for Information Security (BSI) warns of the Folina vulnerability, which could allow an attacker to download an HTML file from the internet using a prepared Word file. This is made possible by the remote template function contained in Microsoft Office. This can be misused for the further execution of PowerShell code. This could allow the attacker to install programmes, display, change or delete data.
Affected versions
It appears to affect Office products 2013, 2016, 2019, 2021 and 365 under Windows 10 and Windows 11 in conjunction with the Microsoft Support Diagnostic Tool (MSDT).
How to protect yourself
Be suspicious of senders you think you know. If you notice a difference between the displayed sender name and the sender address, this is a clear indication of a spam e-mail. Always be careful with file attachments in e-mails (especially Office documents). If in doubt, contact the sender by telephone.
Only open Office documents from trustworthy sources. Be particularly careful with documents in RTF format, as the malicious code can already be executed via the preview in Windows Explorer.
Do you have any questions about emails or IT security? Then please contact the IT Service Desk by email at servicedesk [at] tu-freiberg [dot] de or by telephone on 1818.
Workaround: Deactivate MSDT
As a workaround, Microsoft recommends deactivating the "Microsoft Support Diagnostic Tool" (MSDT).
Note: This is not a final security solution!
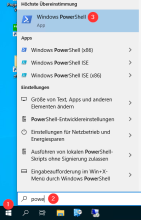
Click on the Windows symbol (1) at the bottom left.
After clicking on (1), simply start typing "power" (2) or search for "Windows Powershell" (3).
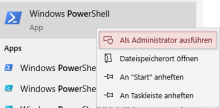
Right-click on "Windows Powershell" and select "Run as administrator".
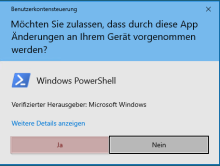
Confirm the following dialogue with "Yes".
You have now started Windows Powershell as an administrator.

Insert the following commands.
New-PSDrive -PSProvider registry -Root HKEY_CLASSES_ROOT -Name HKCR
Remove-Item -Path "HKCR:\ms-msdt" -Recurse

If you receive the following error message, everything is fine:
"The path HKCR:\ms-msdt" cannot be found because it does not exist."
You can now close the Powershell.

For Office 2019
If you are using Office 2019, you must add another command to the previous steps:
Remove-Item -Path "HKCR:\search-ms" -Recurse
The key was successfully deleted with this input and output.

With this error message, everything is OK. In this case, you did not have this key.
Further information
- Zero Day gap in Microsoft Office enables code smuggling
Source: heise.de, 30.05.2022 - Zero Day in Office enables remote code execution
Source: golem.de, 31.05.2022